Layered Defenses and Latent Failures: Why Software Errors Happen
Software errors don’t spring forth from a single bug or an isolated lapse in concentration. They propagate — emerging from a cascade of…
Software errors don’t spring forth from a single bug or an isolated lapse in concentration. They propagate — emerging from a cascade of imperfect defenses across multiple layers: specifications, programmers, programming systems, and finally, the program itself.
Understanding these layers isn’t just an academic exercise. It’s a map of where and how software systems fail — and where we might intervene before the failure becomes real.
Layer 1: Specifications: The First Line of (Theoretical) Defense
Specifications are supposed to be the bedrock: unambiguous, complete, and correct. But often, they are anything but.
A vague specification is like an airport security checkpoint with no metal detectors: it gives the illusion of rigor while letting all kinds of dangerous misunderstandings through. When specs are:
- Ambiguous, they allow multiple, conflicting interpretations.
- Incomplete, they leave critical edge cases open to guesswork.
- Incorrect, they encode faulty assumptions right into the DNA of the system.
The worst part? These flaws are usually latent. They don’t announce themselves until later — when the system is already in motion and unraveling.
Better engineering practices — like rigorous domain modeling, stakeholder alignment, and executable specifications — can reduce this ambiguity. But even the best spec is only as good as the humans interpreting it.
Layer 2: Programmers: Human Firewalls with Faulty RAM
Once the spec is written, it lands in the hands of programmers — humans with experience, intelligence… and cognitive limitations.
While skilled developers often detect inconsistencies or fill in gaps with reasonable defaults, they are still vulnerable to:
- Cognitive overload — juggling multiple concerns without dropping critical ones
- Confirmation bias — assuming their interpretation is correct, even when it’s not
- Misplaced trust — assuming the spec, toolchain, or previous code is more robust than it actually is
This layer can deflect many issues, but it cannot correct upstream failures — especially when it’s being misled by downstream ones.
Layer 3:The Programming System: Tools with Teeth and Traps
Your programming language, compiler, IDE, build system, and libraries form the programming system. This layer is both a blessing and a minefield.
It provides important defenses:
- Syntax checking from compilers
- Autocompletion from IDEs
- Linting and static analysis from external tools
But it also hides many latent usability failures that can sabotage a programmer’s cognition:
- Compilers that give misleading error messages
- Libraries that are inconsistent in their interfaces or error handling
- IDEs that autocomplete you into a bug
This layer amplifies programmer effort — but it also amplifies programmer error when poorly designed.
Layer 4:The Program: Where It All Comes Home to Roost
The final layer is the program itself — the end product, where errors finally take visible form.
By this point, the errors have taken a long journey:
- Perhaps a requirement was miscommunicated.
- Or a mental model was misaligned.
- Or a tool nudged the developer into the wrong fix.
- Or all of the above.
The program holds all of these errors latent — until the right (or wrong) runtime conditions activate them. A bad input. An unexpected state. A misconfiguration. Suddenly, an error that was sleeping through builds and tests becomes a full-blown outage.
Latent Errors Only Fail When Activated
The most insidious thing about software errors is that they don’t manifest until the stars align just right — or wrong. Each layer hides potential failures that might never materialiSe… but might. That’s what makes debugging, testing, and prevention so difficult.
In other words: software doesn’t just fail — it’s set up to fail. The question is whether we catch it before it runs.
So What Can Be Done?
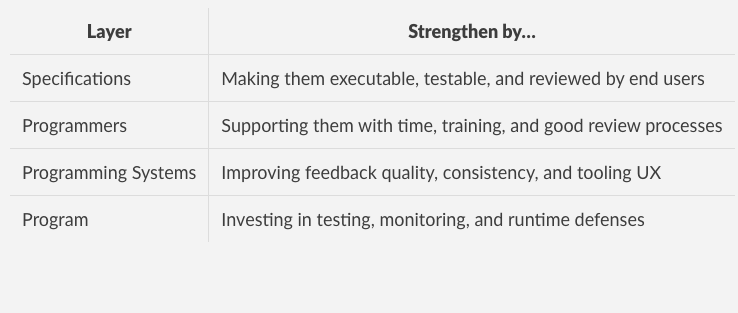
Awareness is the first defense. Here’s a quick summary of how to reinforce each layer:
Each layer has blind spots. But by making each one a little sharper, we reduce the odds that all four align in the worst possible way.
Closing Thought
Software errors don’t emerge from nowhere. They leak through cracks — one layer at a time. Fixing them isn’t about silver bullets. It’s about tightening the defenses at each stage of the journey.
Because while perfect software doesn’t exist, systems with better failure margins do.